SoftEther VPN server setup notes
 Contents
Contents
Following ShadowSocks and V2Ray, I also ran SoftEther VPN. In fact, this was the main one. I found the old notes, so I am putting them here.
What SoftEther VPN is
SoftEther VPN is open-source VPN software from the University of Tsukuba. It supports multiple protocols, including SSL-VPN, L2TP/IPsec, OpenVPN, and MS-SSTP, so you can build a fast and flexible VPN environment.
Compared with ShadowSocks and V2Ray:
- ShadowSocks / V2Ray: proxies, so only selected apps go through them
- SoftEther VPN: a real VPN, so all traffic goes through the tunnel
It also has a GUI management tool, VPN Server Manager, which makes setup relatively easy to understand.
Server setup
These steps are for CentOS 7.
Install dependencies
mkdir -p /usr/local/src/yum/21.softether_server
cd /usr/local/src/yum/21.softether_server
yum --enablerepo=epel --downloadonly --downloaddir=./ install gcc gcc-c++ glibc make binutils zlib openssl readline ncurses zlib-devel openssl-devel readline-devel ncurses-devel psmisc
yum localinstall *.rpmDownload and build SoftEther VPN Server
Check the latest version on the official site: http://jp.softether-download.com/files/softether/
wget http://jp.softether-download.com/files/softether/v4.25-9656-rtm-2018.01.15-tree/Linux/SoftEther_VPN_Server/64bit_-_Intel_x64_or_AMD64/softether-vpnserver-v4.25-9656-rtm-2018.01.15-linux-x64-64bit.tar.gz
tar xvfz softether-vpnserver-v4.25-9656-rtm-2018.01.15-linux-x64-64bit.tar.gz
cd vpnserver
make
# proceed with 1 -> 1 -> 1
cd ..
mv vpnserver /usr/local/
cd /usr/local/vpnserver/Create an autostart script
Create /etc/init.d/vpnserver:
#!/bin/sh
# chkconfig: 2345 99 01
# description: SoftEther VPN Server
DAEMON=/usr/local/vpnserver/vpnserver
LOCK=/var/lock/subsys/vpnserver
test -x $DAEMON || exit 0
case "$1" in
start)
$DAEMON start
touch $LOCK
;;
stop)
$DAEMON stop
rm $LOCK
;;
restart)
$DAEMON stop
sleep 3
$DAEMON start
;;
*)
echo "Usage: $0 {start|stop|restart}"
exit 1
esac
exit 0chmod 755 /etc/init.d/vpnserver
/sbin/chkconfig --add vpnserver
/etc/init.d/vpnserver startKernel parameters for IPsec
Create /etc/sysctl.d/60-ipsec.conf:
net.ipv4.ip_forward = 1
net.ipv4.conf.all.accept_redirects = 0
net.ipv4.conf.all.rp_filter = 0
net.ipv4.conf.all.send_redirects = 0
net.ipv4.conf.default.accept_redirects = 0
net.ipv4.conf.default.rp_filter = 0
net.ipv4.conf.default.send_redirects = 0
net.ipv4.conf.eth0.accept_redirects = 0
net.ipv4.conf.eth0.rp_filter = 0
net.ipv4.conf.eth0.send_redirects = 0
net.ipv4.conf.lo.accept_redirects = 0
net.ipv4.conf.lo.rp_filter = 0
net.ipv4.conf.lo.send_redirects = 0Apply it:
sysctl -p /etc/sysctl.d/60-ipsec.confFirewall
If you use firewalld, open the VPN service ports.
Create /etc/firewalld/services/vpnserver.xml:
<?xml version="1.0" encoding="utf-8"?>
<service>
<short>VPN</short>
<description>SoftEther VPN Server</description>
<port protocol="tcp" port="443"/>
<port protocol="tcp" port="992"/>
<port protocol="tcp" port="1194"/>
<port protocol="tcp" port="5555"/>
<port protocol="udp" port="1194"/>
<port protocol="udp" port="500"/>
<port protocol="udp" port="4500"/>
</service>firewall-cmd --add-service=vpnserver --zone=public --permanent
firewall-cmd --add-service=ipsec --zone=public --permanent
firewall-cmd --reloadOr disable firewalld, which is what I used at the time:
systemctl stop firewalld
systemctl disable firewalldGUI setup in VPN Server Manager
After the server is up, connect from Windows VPN Server Manager and configure it there.
SecureNAT
SecureNAT keeps NAT and DHCP entirely inside SoftEther, without needing a physical bridge. Since you do not need routing on the server side, it is convenient.
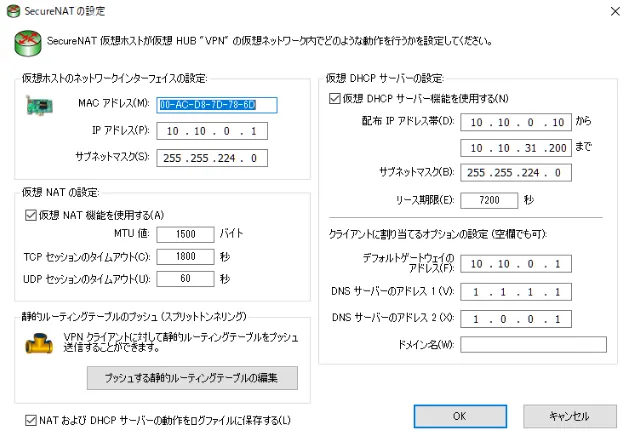
Virtual host (NAT gateway)
- IP address:
10.10.0.1 - Subnet mask:
255.255.224.0(/19)
Virtual DHCP server
- Allocation range:
10.10.0.10to10.10.31.200 - Lease time: 7200 seconds (2 hours)
- DNS:
1.1.1.1,1.0.0.1(Cloudflare DNS)
Group security policy
Set restrictions for service use.
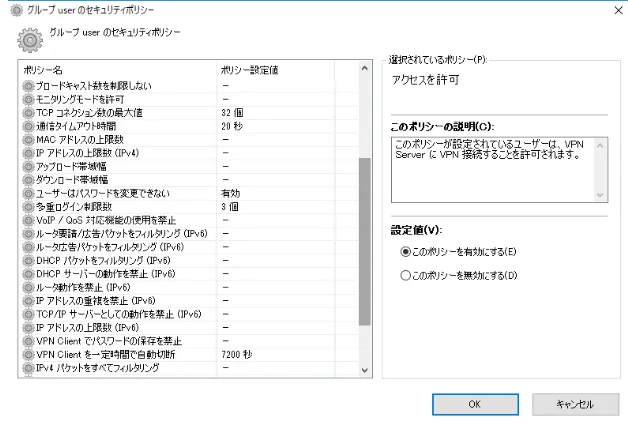
Main settings
- Maximum TCP connections: 32
- Communication timeout: 20 seconds
- Users cannot change passwords: enabled
- Maximum simultaneous logins: 3
- Auto-disconnect VPN clients after a fixed time: 7200 seconds (2 hours)
User management with vpncmd
GUI works, but if you manage many users, scripting through vpncmd is more efficient.
# Fetch and run a user-creation script
wget -O accounts https://example.com/api/get/accounts/1
/usr/local/vpnserver/vpncmd /server localhost:5555 /in:accountsThe script looks like this:
Hub VPN
UserCreate user001 /GROUP:none /REALNAME:none /NOTE:none
UserPasswordSet user001 /PASSWORD:password001
UserCreate user002 /GROUP:none /REALNAME:none /NOTE:none
UserPasswordSet user002 /PASSWORD:password002Recommended settings in 2025
The old setup worked, but if I were doing it now, I would change a few things.
Cipher suite
SoftEther defaults to AES128-SHA, but I would now recommend AES256-GCM-SHA384. It is a TLS 1.3-based, safer cipher suite.
You can change it in VPN Server Manager under Server Settings -> Encryption and communication.
Authentication
For service use, I would prefer certificate-based authentication over password authentication.
L2TP/IPsec
Microsoft deprecated L2TP/IPsec in 2024. If I were building from scratch now, I would prioritize SSL-VPN (SoftEther’s own protocol) or OpenVPN.
Security audit
SoftEther was audited once in 2017, but not since then. If security matters, it is worth considering alternatives such as WireGuard.
-> Continue with: WireGuard VPN server setup notes
-> Summary: Comparison of VPN protocols for China-facing connectivity